What is Dell Data Protection encryption?
Dell Encryption is a number of applications that allow you to: Detect data security risks on desktops, laptops, and external media. Protect data on these devices by enforcing access control policies, authentication, and encryption of sensitive data.
How do I decrypt Dell Data Protection encryption?
To decrypt the device:
- Log in to the Windows computer.
- In the Windows System Tray, right-click the Dell Data Protection | Encryption icon and then select Open Dell Data Protection | Encryption.
What is Dell Data Protection Access?
Dell Data Protection | Access (DDP|A) is an integrated end point security management suite. It provides for seamless data security and authentication. It allows you to authenticate using a fingerprint, smartcard, contactless smartcard or password.
How do I know if my Dell is encrypted?
Log into the Windows system. In the Windows System Tray, right-click the Dell Encryption (formerly Dell Data Protection | Encryption) icon and then select Open Dell Encryption/Open Dell Data Protection | Encryption.
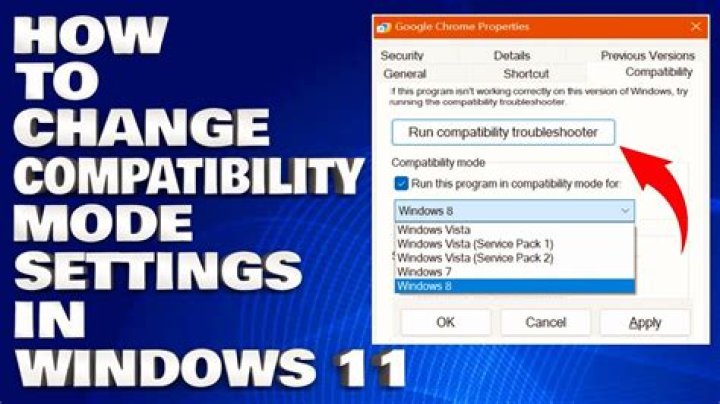
How do I encrypt my Dell laptop?
Manual Device Encryption Click the Start button, select Settings > Update & Security > Device Encryption. If device encryption is turned off, click select Turn on. You are prompted to back up your recovery key. Dell recommends saving the recovery key to USB drive and not to the system drive.
How do I update Dell encryption?
Log in to the Windows computer. In the Windows System Tray, right-click the Dell Encryption (formerly Dell Data Protection | Encryption) icon and then select Check for Policy Updates.
How do I uninstall Dell Encryption Enterprise?
In terminal, type sudo /Library/Dell/Dell\ Encryption\ Enterprise/Dell\ Encryption\ Enterprise. app/Contents/Resources/Scripts/uninstall. sh and then press Enter. Enter the credentials for an account with sudo rights and then press Enter.
How do I know if Dell Data Protection is installed?
To find out if Dell Data Protection Encryption is installed on your Windows laptop, go to the System Tray and see if the Dell Data Protection Encryption icon is displayed. The Dell Data Protection Encryption icon is circled in red in the picture below. If the icon is present, then the software is installed.
What do you know about data protection?
Data protection is about ensuring people can trust you to use their data fairly and responsibly. If you collect information about individuals for any reason other than your own personal, family or household purposes, you need to comply.
Do I need device encryption?
When storing and accessing confidential information on laptops and mobile devices, it is essential to encrypt them. Device encryption is the process of scrambling data into illegible code and making it indecipherable to anyone without a password or a recovery key.
How do you uninstall Dell Data Protection?
Go to Settings > Control Panel > Uninstall a program. Find out where Dell Data Protection | Security Tools Authentication is in the program list. Right click on the program name, click Uninstall option to activate the default uninstaller. Follow the instruction to proceed. Restart your PC after the process finished.
What is Dell encryption?
Dell Data Protection Encryption supports Advanced Encryption Standard (AES) with 128-bit and 256-bit keys. 128-bit is the minimum recommended key size for FDE, and 256-bit is the preferred key strength, so the key sizes provide sufficient protection against today’s threats (128-bit) and tomorrow’s (256-bit).
What is encryption protection?
Encryption is used to protect data stored on a system (encryption in place or encryption at rest); many internet protocols define mechanisms for encrypting data moving from one system to another (data in transit).
What is a data encryption key?
An encryption key is a random string of bits created explicitly for scrambling and unscrambling data. Encryption keys are designed with algorithms intended to ensure that every key is unpredictable and unique. The longer the key built in this manner, the harder it is to crack the encryption code.